Having the right technology controls in place can vastly impact the cost of cyber insurance and claims eligibility.
Hackers are aggressively targeting small and medium-sized businesses: One in every three SMBs was hit with ransomware in 2024, according to research from Microsoft.
The luckiest businesses will never get breached or will have the incident response and backup and recovery plans in place to walk away unscathed. But even they are at risk of liabilities such as business disruptions, exposed data and fines. Not to mention, 94% of all ransomware attempts against SMBs in 2024 targeted backups, according to Sophos.
Enter cyber insurance. As more SMBs investigate first- and third-party coverage, they’ll encounter a slew of technical prerequisites. It’s crucial that they know what risks to cover and the requirements to qualify for that coverage in order to ultimately be eligible for a payout.
Upfront Risk Assessments Save Time and Money
Many cyber insurance providers provide free risk assessments for businesses, but John Candillo, field CISO at CDW, recommends doing a little upfront work to smooth out the process and avoid getting blindsided.
“Insurers want to know how your business looks from the outside looking in,” he says. “A focus on this ahead of time can greatly improve your situation when it comes to who’s willing to underwrite your policy, but also what your premiums are going to be and how you’re answering questionnaires,”
Conducting an internal risk assessment and engaging with cybersecurity ratings companies such as SecurityScorecard or Bitsight can help SMBs be more informed policy shoppers.
“If you understand what the auditor is going to ask you and you’re prepared for it, the results of the audit are going to be way different than if you’re caught off guard,” Candillo says.
These steps get stakeholders thinking about what type of risk requires coverage. Cyber insurance can broadly be put into two categories. First-party coverage will protect against things such as breach response costs, cyber extortion costs, data-loss costs and business interruptions. Third-party coverage insures against risks such as breach liabilities and regulatory penalties.
The more you know up front about your risk profile, the easier it is to advocate for yourself during the underwriting process.
Proper Security Controls Are Necessary for Coverage
Inadequate cybersecurity controls can be a dealbreaker for cyber insurers, resulting in outright rejection or prohibitively expensive premiums.
“They’re going to have anywhere from 15 to 30 controls they’re going to ask about,” Candillo says. “But we call the most common things they ask about the big 12.”
- Multifactor authentication
- Privileged access management
- Remote access controls (such as VPNs)
- Endpoint protection and response
- Security information and event management
- Incident response plan
- Business continuity plan and disaster recovery
- Backup strategy
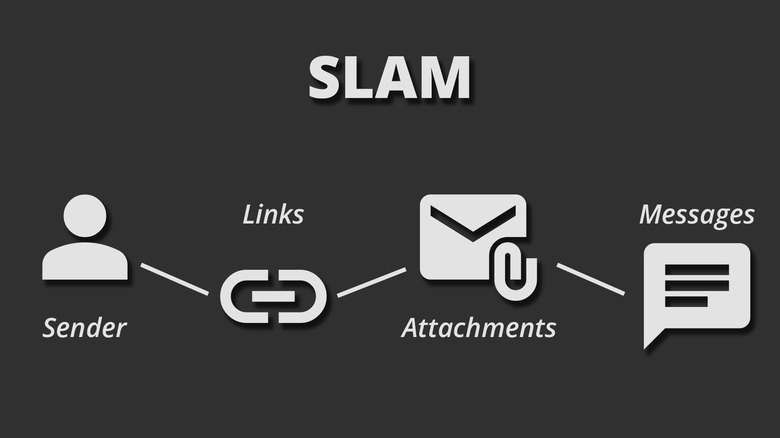
- Email security
- Security awareness training
- Third-party risk management
- Patching and vulnerability management
“They’re going to ask you no very pointed questions,” Candillo says. “For example: Is every application accessible only through multifactor authentication? And they’re going to expect a yes or no answer.”
Phrases such as “yes, no, always, never, every and all” fall into a category Cardillo calls absolutist language. Covering your bases isn’t just a matter of getting coverage; it’s also a matter of meeting certain requirements should you need to submit a claim.
“Don’t just answer yes or no,” Candillo says. “Take the PDF they gave you with the yes or no questions, export it into another format where you can actually qualify your answers and give as much information as possible.”
This added context helps businesses have a more complete picture of the controls they have in place and can round out answers in questionnaires as a possible defense in the event that an insurer attempts to deny a claim.
In terms of implementing the prerequisite technology, Candillo recommends working with a partner such as CDW with access to solutions from a variety of vendors.
“There are cheap ways to do it and there are expensive ways to do it,” he says. “SMBs are probably going to opt for the affordable way, as long as they know what that looks like.”
Cyber Insurance Isn’t a One-Time Thing
Most cyber insurance policies will need to be reviewed on an annual basis. Businesses will therefore have to complete questionnaires annually, and the questions being asked could change depending on shifting conditions in the threat landscape.
What’s more, many businesses will create an “insurance tower,” as they may require more than one insurer to achieve the desired level of coverage. While a common practice, this does multiply the work that goes into renewing policies each year. Candillo says this further underscores the importance of adding context to checklists.
“It’s something they have to deal with every year, and you may only hear about it once a year,” he says. “Without that additional context, it’s hard to get a lot of knowledge and experience around how the answers you give impact insurability, not to mention premiums.”
If you are looking for an expert to help you find the best solutions for your business talk to GCInfotech about a free technology assessment
Published with consideration from BizTechMagazine.com SOURCE