The jargon around cybersecurity is cryptic and confusing, which is exactly what criminals want. But understanding these terms can help you keep safe.
The cyberspace is filled with terms that either look the same, sound the same, or mean the same (but are not identical).
Knowing the difference between these similar terms can be tricky, especially when you’ve to keep up with all the common terminologies and principles used in the security domain. Add to it the constant innovation and change happening within cybersecurity, and you’ve got a whole set of complex terms that you need to understand and constantly learn about.
So, here are some similar security terms that are often confused and misused.
Security vs. Privacy

Online security and privacy go hand-in-hand. They are used interchangeably during discussions because they sometimes overlap in today’s connected world.
But there are some key differences between the terms when used in the cybersecurity context.
- Security: Security refers to the protection of your personal information from malicious threats. It can include any information that can be used to determine your identity.
- Privacy: Privacy refers to the rights or control you have on your information and the way it’s used.
While security is concerned with preventing unauthorized access to data, privacy focuses on ensuring that personal information is collected, processed, and transmitted compliantly and with the owner’s consent. In simple terms, security protects your data while privacy protects your identity.
To achieve security and privacy, organizations use tools and techniques such as firewalls, encryption protocols, network limitations, and different authentication and authorization techniques.
Authentication vs. Authorization

Authentication and authorization are similar-sounding security concepts within the scope of user identity and access management. Here’s how the two differ.
- Authentication: User authentication is the process of verifying that users are who they claim to be. It relates to identifying users’ identity.
- Authorization: Authorization is an act of establishing a user’s rights and privileges. It verifies what specific files, applications, and resources a user has access to.
Authentication is achieved using passwords, PINs, fingerprints, facial recognition, or other forms of biometric information. It’s visible and can be partially changed by the user.
Authorization, on the other hand, works through access management settings implemented and maintained by an organization. They aren’t visible and can’t be changed by the end user.
In a secure environment, authorization always takes place after user authentication. Once a user is verified, they can access different resources based on the permissions set by the organization.
Data Breach vs. Identity Theft

It’s easy to get confused between a data breach and identity theft, as the two are closely connected. The threat for users and the outcome is the same either way; that is, sensitive information is compromised. But there are some differences.
- Data Breach: A data breach refers to a security incident where confidential data is accessed without authorization of the owner.
- Identity Theft: When a cybercriminal uses your personal information, such as ID or social security number, without your permission, it constitutes an identity theft.
A data breach occurs when a cybercriminal hacks into a system you’ve entrusted with your information or a company that has your personal information anyway. Once a breach occurs, criminals can use your private information to open an account or commit financial fraud in your name.
The main difference between a data breach and theft is in terms of the damage caused by the incidents. The implications of a breach are usually far more damning compared to an identity theft. According to a report by the US Securities and Exchange Commission, 60 percent of small businesses don’t survive a breach.
However, the damages caused by identity theft can be highly consequential too. The impact of misusing identity go beyond forged checks, fake credit cards, and insurance frauds, and can even endanger national security.
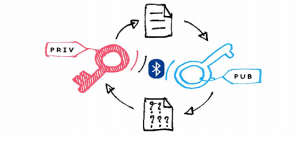
Encryption vs. Encoding vs. Hashing
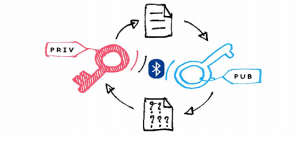
Encryption, encoding, and hashing are data security terms often used interchangeably and incorrectly. There’s a lot of difference between these terms and it’s important to know these differences.
- Encryption: It’s a process used to convert readable data, also called plain text, into unreadable data, called cipher text. The data can only be decrypted back to plain text using the appropriate encryption key.
- Encoding: Encoding is a process in which data is changed from one format to another using an algorithm. The aim is to transform data into a form that is readable by most of the systems.
- Hashing: Hashing is an irreversible cryptographic process used to convert input data of any length into a fixed size string of text using a mathematical function.
This means that any text can be converted into an array of letters and numbers through an algorithm. The data to be hashed is called input, the algorithm used in the process is called a hash function, and the result is a hash value.
Encryption, encoding, and hashing differ in terms of functionality and purpose. While encryption is meant to ensure confidentiality, encoding focuses on data usability. Hashing, on the other hand, ensures authenticity by verifying that a piece of data hasn’t been altered.
VPN vs. Proxy
VPNs and proxies are both used to change your online location and stay private. They have some overlap, but the differences are quite apparent.
- VPN: A VPN, short for Virtual Private Network, is a discrete program that changes your geo-location and reroutes your entire internet traffic through servers run by the VPN provider.
- Proxy: A proxy server is a browser extension that changes your IP address to unblock geo-restricted web pages, but doesn’t offer the extra protection of a VPN.
The main difference between a proxy and VPN is that a proxy server only changes your IP address and doesn’t encrypt your web activities. Secondly, unlike a VPN, a proxy only redirects traffic within the browser. Data from other applications connected to the internet won’t be routed through the proxy.
Spam vs. Phishing vs. Spoofing

Spam, phishing, and spoofing are social engineering tactics used to lure users into revealing personal information.
- Spam: Spam is any unwanted junk emails, instant messages, or social media messages sent out to a wholesale recipient list. Spam is usually sent for commercial purposes and can be damaging if you open or respond to it.
- Phishing: Phishing is an unsolicited email designed to harm users by obtaining personal information like usernames, passwords, and even bank details. A phishing email looks like it comes from a legitimate source, but is intended to trick users into clicking on a link containing malware.
- Spoofing: Spoofing is a subset of phishing attacks in which the attacker impersonates an individual or organization with the intent to gain personal and business information.
Phishing aims to gain personal information by convincing users to provide it directly while spoofing disguises an identity to steal information. The two are closely paired as both involve a level of misrepresentation and masquerading.
Better Understanding, Better Protection
Cybersecurity terminologies and concepts evolve almost as rapidly as memes on the internet. A lot of these terms sound similar but mean something different when you dig a little deeper.
Learning the key terms and their differences will help you better understand and effectively communicate your cybersecurity needs.
If you are looking for an expert to help you find the best solutions for your business talk to GCInfotech about a free technology assessment
Published with consideration from makeuseof.com SOURCE