Unexpected disruptions, such as natural disasters and cyberattacks, can knock your business off course. Thus, it’s critical to develop a strong business continuity plan (BCP), but having one isn’t enough. How you create, maintain, and execute it is just as important. Unfortunately, many businesses make avoidable mistakes during the planning process that leave them vulnerable in a crisis.
Below are the top pitfalls businesses face when crafting their continuity strategies, along with practical ways to avoid them:
Skipping a thorough risk review
Business owners tend to zero in on one or two risks, such as cyberattacks, while overlooking others, including severe weather, supply chain disruptions, or staffing shortages. These oversights can leave their BCPs unprepared, making their operations vulnerable. To prevent this, conduct a comprehensive risk assessment that identifies all potential threats and their impact on your business.
Failing to prepare the team
Your business continuity plan is only effective if employees know how to carry it out. That said, a smooth response during a crisis depends on everyone understanding their roles. Through regular training sessions, walkthroughs, and drills, you can reinforce that understanding and build the confidence to act under pressure.
Not testing the plan in realistic scenarios
Businesses often create a BCP and set it aside, assuming it will work as intended during a disruption. However, unless you test it with realistic simulations or mock incidents, there’s no way to know how well it will actually hold up. That’s why routine testing is vital; it helps reveal gaps, refine processes, and confirm the plan’s feasibility.
Underestimating your tech reliance
Technology drives nearly every part of modern business, from internal communication and sales to logistics and customer service. However, many organizations overlook just how dependent they are on specific systems, software, or data. Failing to account for this reliance can leave you unprepared when an important platform goes down.
You can avoid this by identifying your mission-critical systems and putting clear contingency plans in place. Whether it’s a data backup platform, a manual workaround, or a preconfigured recovery setup, document your measures in your BCP.
Poor communication planning
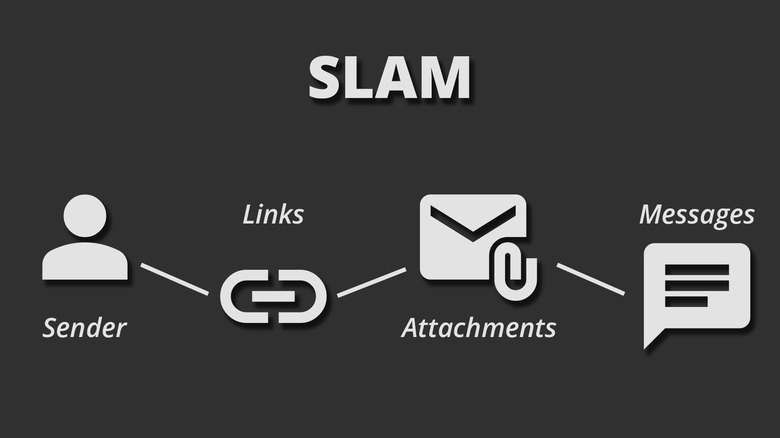
In the event of an emergency, effective communication is key to executing a strong response. Without a clear strategy for keeping staff, vendors, customers, and stakeholders informed, confusion can spread quickly. Thus, to keep everyone on the same page, define a communication chain and prepare reliable channels, such as group messaging platforms, SMS alerts, automated call trees, or dedicated emergency apps.
Ignoring your supply chain
Suppliers and vendors are vital to your operations, yet they’re often left out of business continuity planning. This oversight can have serious financial consequences. Consider a manufacturer that relies on a single supplier for a critical part. If that supplier goes offline, that production line grinds to a halt, resulting in missed deadlines and lost revenue.
You can reduce such risks by including suppliers in your continuity strategy. That means establishing clear communication protocols for disruptions, understanding each partner’s recovery timeline, and lining up backup vendors if necessary.
Relying too heavily on insurance
Insurance can support recovery after a disaster, but it won’t prevent operational disruptions or financial losses. Even more concerning, many businesses assume they’re fully covered, only to realize too late that their policies don’t cover key risks. To avoid surprises, review your policies regularly to ensure coverage aligns with how your business actually operates and the risks it faces.
Making the plan too complicated
When every second counts, simplicity matters. A business continuity plan full of jargon and complex flowcharts might seem comprehensive, but it’s useless if your team can’t understand it. Focus on clarity and ease of execution to ensure the plan works when it’s needed most.
Letting the plan get outdated
A business continuity plan that worked last year may no longer be effective. As your business evolves — with new systems, additional users, or expanded services — its needs change. On top of that, new threats can emerge at any time. Therefore, it’s important to revisit your BCP, especially after major organizational or environmental changes, to make sure it still addresses your new risks and priorities.
A business continuity plan is your company’s lifeline during uncertain times, but even small mistakes can weaken it. By avoiding these common pitfalls, you create a plan that’s not only comprehensive but truly reliable when it matters most.
If you are looking for an expert to help you find the best solutions for your business talk to GCInfotech about a free technology assessment
Published with consideration from TechAdvisory.org SOURCE