If you’re struggling to juggle your passwords, the solution to your woes is a password manager. See our recommendations.
Password managers are a safe, secure way of logging into your various online accounts. In fact, they’re vastly preferable to the alternatives of either trying to remember multiple unique passwords or re-using the same password over and over.
According to Pew Research Centre, half of users have up to 25 password-protected accounts online. That’s far too many for the average person to remember, making it hard to stay secure. A secure password manager will automatically store all your logins, meaning that you’ll never have to remember one ever again, and can even generate passwords for you.
Given that even industry-leader LastPass was once the victim of a hack, concerns remain over using password managers. Besides, you may be questioning the wisdom of storing all your passwords in one place. These are legitimate concerns, but research has shown that using a password manager is far more secure than not using one. The risk of your business getting hacked is high, particularly during the pandemic, so we’d strongly recommend getting one yourself.
As for which password manager you should choose? We’ve tested some of the best password managers around, and while they’re all safe and secure, the best on test was LastPass. This stands out thanks to a simple interface, secure setup, and brilliant family-sharing options. Plus, you can try LastPass for free to see if you like it.
Is it Safe to Use a Password Manager?
Yes – a good quality password manager is a safe, trustworthy and highly recommended security tool. In fact, security experts almost uniformly believe that password managers are infinitely safer than virtually every alternative there is, for businesses and individuals alike.
Top password managers, such as 1Password, Dashlane or LastPass, can be trusted to protect your account logins thanks to secure encryption that keeps your passwords secret.
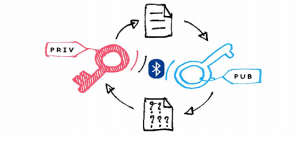
Here’s how it works in practice. You create an account with a password manager, then create a single “master password” to log into it. To keep your password manager safe to use, it’s essential that your master password isn’t anything obvious. So that’s no to “12345,” “qwerty,” or “passwd.” Instead, pick a longer phrase or mix and match cases and special characters – just ensure it’s unique and memorable.
Then, the password manager can get to work automatically generating complex, unique passwords for every service you log into online – one for your Amazon account, email account, Facebook account and so on. You won’t need to memorize these – whenever you login in, the password manager will automatically apply the password (and you enable the password manager via that single master password).
This entire process is far more secure than re-using the same password over and over on multiple sites – the single biggest risk you can take with you and your business’ online security. It’s also far easier than attempting to remember multiple unique passwords.
So, if it’s all win, why are there any questions around password manager safety? Largely, these come down to an understandable concern over the security of handing over your logins to a third-party service. That’s why we’d recommend only using a trustworthy, well-rated password manager. So which ones would we recommend?
Most Secure Password Manager
If you want a secure password manager, you should opt for a paid one. Free password managers tend to be restricted in some way, and are usually supported with adverts. Additionally, free password managers are simply not set up to handle a full business’ security needs, which means paid for is always the way to go.
In our testing, we found LastPass to be the most secure password manager. For a few dollars a month, it could save you a lot of headaches, as well as time spent waiting for password reminder emails to drop into your inbox.
Do Password Managers Get Hacked?
No online system is infallible. Password managers – just like any other online service you use, such as Amazon, Twitter or Facebook – run the risk of being hacked. In fact, some have been.
The best password managers, however, will take your security very seriously – after all, you’re paying for the service. If you lose trust in them, they lose your patronage, and with it, your payment.
When LastPass was hacked in 2015, users were right to be concerned – after all, if a hacker could get into the system, they could, in theory, have access to every password that LastPass users had stored there. However, even though its security was breached, hackers were unable to steal any information – all of the passwords were protected by the users’ Master Password, which is not stored on the LastPass servers. This meant that the encryption on the passwords stored by LastPass was unable to be cracked. And that is why you should pay for a password manager.
Password managers are also a common target for ‘ethical hackers’ — those who like to test the security of online systems to flex their coding muscles. Password managers are their white whale – crack one of these open, and they’ll win the acclaim of the industry.
This isn’t as scary as it sounds though. In fact, ethical hackers are offering a great service, finding exploits in online systems before more nefarious people do. Once they’ve found a vulnerability, these hacklers will make contact with the service and let them know, allowing the provider to then fix the issue.
Verdict – Should You Use a Password Manager?
We can’t state this clearly enough – a password manager is a safe, recommended way to secure your online logins. The alternatives are far, far riskier – in particular, that old habit of re-using the same old password again and again across multiple websites (please, just don’t).
No system is guaranteed bullet-proof, and as the LastPass hack showed, even password managers can be vulnerable. However, as that very incident showed, there are serious protections in place, and these prevented the LastPass hack from being a disaster for any customers.
In the age of hybrid work and vast security breaches, we’d strongly recommend getting up and running with a password manager for proper online peace of mind.
If you are looking for an expert to help you find the best solutions for your business talk to GCInfotech about a free technology assessment
Published with consideration from Tech.co SOURCE